Cyber intel researchers of SentinelOne discover Turkish espionage campaign
The campaign nicknamed EGoManiac that targeted citizens was conducted from 2010 to 2016 by Turkish officials, in what seems to have been part of the political struggle in the country
Cybertech
| 13/09/2021
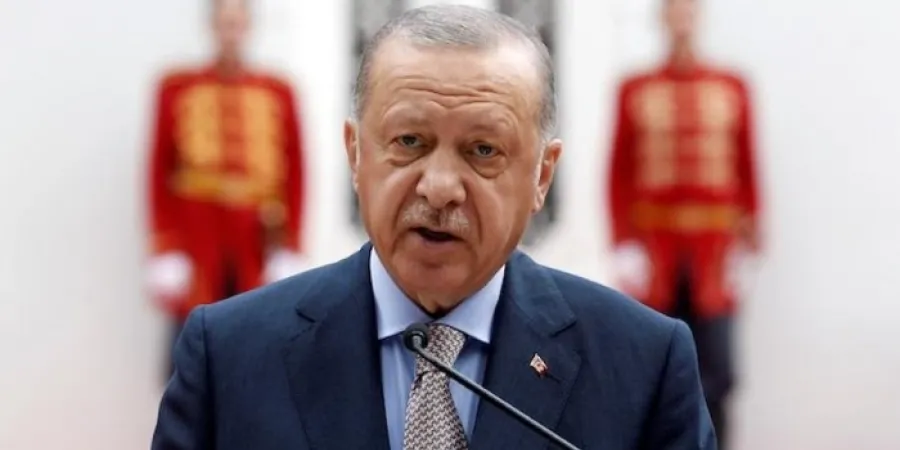
In February 2011 the Turkish Police raided the office of the popular news website OdaTV, which was identified with the opposition to then Prime Minister (and current President) Recep Tayyip Erdogan, and confiscated computer equipment. Documents were found on the computers of some of the reporters and editors that appeared to connect them to a secret network called Ergenekon, a sort of underground (although it is not clear whether it is real) purportedly connected to the Turkish "deep state".
About 12 journalists were arrested and placed under house arrest for a year, but they were ultimately acquitted in 2017 after a long process. During the whole time, the journalists claimed that the documents were fake and that they had been planted in their computers via e-mail or physical access to their computers by entities that wanted to frame them. Investigations conducted by independent entities found malware in code on the computers, but were not able to prove that there was a conspiracy to incriminate the journalists.
Researchers from cyber company SentinelOne reexamined the digital evidence and came across some surprising findings. According to the company, it turns out that the cyberattack tools used against the journalists were supplied by the Italian spyware manufacturer Hacking Team, which has been accused of selling spyware to governments for the purpose of espionage against opposition figures.
Examination of documents from Hacking Team – which were publicly leaked online in 2015, revealing the company's connections to dubious entities worldwide, including drug cartels in Mexico – showed that Hacking Team did indeed sell spyware to entities in Turkey, but not to official government entities. In a deal through a straw company in the Persian Gulf, the company sold its Remote Control System (RCS) spyware to a company from Istanbul called Datalink Analiz. The researchers believe that it is a company linked to Islamist entities and the AKP party of Erdogan, who was prime minister at that time.
Thus, the researchers estimate that entities that supported Erdogan sought to acquire advanced espionage tools, which are only sold to governments, in order to strengthen Erdogan's position before he ran for president. They contacted Hacking Team, while impersonating official entities, fraudulently acquired the software, and then used it for political purposes.
The research report can be found here.
The campaign nicknamed EGoManiac that targeted citizens was conducted from 2010 to 2016 by Turkish officials, in what seems to have been part of the political struggle in the country
In February 2011 the Turkish Police raided the office of the popular news website OdaTV, which was identified with the opposition to then Prime Minister (and current President) Recep Tayyip Erdogan, and confiscated computer equipment. Documents were found on the computers of some of the reporters and editors that appeared to connect them to a secret network called Ergenekon, a sort of underground (although it is not clear whether it is real) purportedly connected to the Turkish "deep state".
About 12 journalists were arrested and placed under house arrest for a year, but they were ultimately acquitted in 2017 after a long process. During the whole time, the journalists claimed that the documents were fake and that they had been planted in their computers via e-mail or physical access to their computers by entities that wanted to frame them. Investigations conducted by independent entities found malware in code on the computers, but were not able to prove that there was a conspiracy to incriminate the journalists.
Researchers from cyber company SentinelOne reexamined the digital evidence and came across some surprising findings. According to the company, it turns out that the cyberattack tools used against the journalists were supplied by the Italian spyware manufacturer Hacking Team, which has been accused of selling spyware to governments for the purpose of espionage against opposition figures.
Examination of documents from Hacking Team – which were publicly leaked online in 2015, revealing the company's connections to dubious entities worldwide, including drug cartels in Mexico – showed that Hacking Team did indeed sell spyware to entities in Turkey, but not to official government entities. In a deal through a straw company in the Persian Gulf, the company sold its Remote Control System (RCS) spyware to a company from Istanbul called Datalink Analiz. The researchers believe that it is a company linked to Islamist entities and the AKP party of Erdogan, who was prime minister at that time.
Thus, the researchers estimate that entities that supported Erdogan sought to acquire advanced espionage tools, which are only sold to governments, in order to strengthen Erdogan's position before he ran for president. They contacted Hacking Team, while impersonating official entities, fraudulently acquired the software, and then used it for political purposes.
The research report can be found here.