Russian Hacking Group Claims to Have Infiltrated Major US Antivirus Companies
Ami Rojkes Dombe
| 14/05/2019
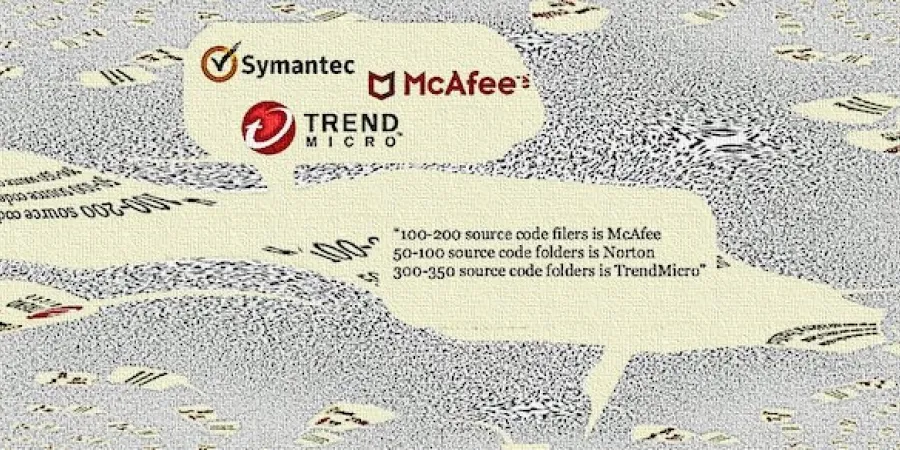
Threat-research firm Advanced Intelligence (AdvIntel) reported last week that a Russian hacking collective known as Fxmsp has compromised the networks of three major US antivirus vendors and offered to sell their stolen source code for $300,000.
On Monday, BleepingComputer reported it had obtained evidence from AdvIntel showing communication from the Fxmsp group naming three of the victims: Symantec, McAfee, and Trend Micro. the evidence included full chat logs listing all the three identified anti-virus names (and more) breached as disclosed by the actor; full video recording from the actor assets regarding their operation;
and full source code samples from at least one of the AV vendors breached as obtained from the actor.
“The company [AdvIntel] also sent us a screenshot showing the properties of a video file to support their findings. According to AdvIntel, the video shows content from the hop server and transfer of gigabytes of data from the compromised antivirus company, with file timestamps, actor commentary, source code, and walkthrough of the actual code.”
In response to BleepingComputer’s request, the three companies sent the following statements:
Symantec: “Symantec is aware of recent claims that a number of US-based antivirus companies have been breached. We have been in contact with researchers at AdvIntel, who confirmed that Symantec (Norton) has not been impacted. We do not believe there is reason for our customers to be concerned.”
Trend Micro: “We have an active investigation underway related to recent claims, and while it is not complete, we want to transparently share what we have learned. Working closely with law enforcement, our global threat research and forensic teams are leading this investigation. At this moment, we are aware that unauthorized access had been made to a single testing lab network by a third party and some low-risk debugging related information was obtained. We are nearing the end of our investigation and at this time we have seen no indication that any customer data nor source code were accessed or exfiltrated.
“Immediate action was taken to quarantine the lab and additionally secure all corresponding environments. Due to the active nature of the investigation, we are not in a position to share any additional information, but we will provide an update when additional insights become available and can be disclosed.”
McAfee: “McAfee is aware of this threat claim targeting the industry. We’ve taken necessary steps to monitor for and investigate it.”
Threat-research firm Advanced Intelligence (AdvIntel) reported last week that a Russian hacking collective known as Fxmsp has compromised the networks of three major US antivirus vendors and offered to sell their stolen source code for $300,000.
On Monday, BleepingComputer reported it had obtained evidence from AdvIntel showing communication from the Fxmsp group naming three of the victims: Symantec, McAfee, and Trend Micro. the evidence included full chat logs listing all the three identified anti-virus names (and more) breached as disclosed by the actor; full video recording from the actor assets regarding their operation;
and full source code samples from at least one of the AV vendors breached as obtained from the actor.
“The company [AdvIntel] also sent us a screenshot showing the properties of a video file to support their findings. According to AdvIntel, the video shows content from the hop server and transfer of gigabytes of data from the compromised antivirus company, with file timestamps, actor commentary, source code, and walkthrough of the actual code.”
In response to BleepingComputer’s request, the three companies sent the following statements:
Symantec: “Symantec is aware of recent claims that a number of US-based antivirus companies have been breached. We have been in contact with researchers at AdvIntel, who confirmed that Symantec (Norton) has not been impacted. We do not believe there is reason for our customers to be concerned.”
Trend Micro: “We have an active investigation underway related to recent claims, and while it is not complete, we want to transparently share what we have learned. Working closely with law enforcement, our global threat research and forensic teams are leading this investigation. At this moment, we are aware that unauthorized access had been made to a single testing lab network by a third party and some low-risk debugging related information was obtained. We are nearing the end of our investigation and at this time we have seen no indication that any customer data nor source code were accessed or exfiltrated.
“Immediate action was taken to quarantine the lab and additionally secure all corresponding environments. Due to the active nature of the investigation, we are not in a position to share any additional information, but we will provide an update when additional insights become available and can be disclosed.”
McAfee: “McAfee is aware of this threat claim targeting the industry. We’ve taken necessary steps to monitor for and investigate it.”