Forget the Other Vulnerability Hunting Software Products, Zerodium Offers up to $2M per Exploit
Ami Rojkes Dombe
| 10/01/2019
Bug Bounty vulnerability hunting software products pay nice rewards, but nothing like the amounts offered by Zerodium – the zero-day exploit vendor. The company sells vulnerabilities as a permit, thereby reducing the vulnerability/exploit cost for the end user.
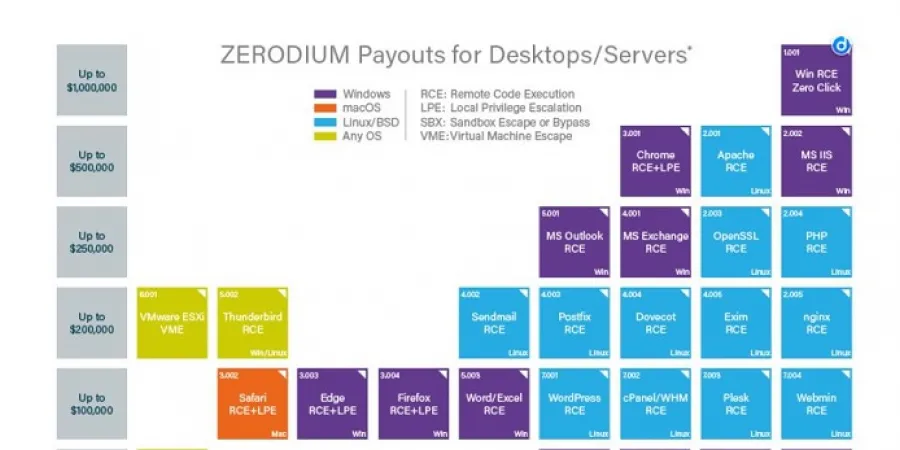
The latest announcement regarding the platform provided a price list for exploits. Well, the price for an Apple iOS remote jailbreak (zero-click) with persistence amounts to two million dollars. The same exploit with one click will produce $1.5 million. An exploit for WhatsApp will produce a million dollars and an exploit for Chrome or Safari will produce about $500,000. An exploit for Windows will produce a million dollars. The company undertakes to pay within one week of the moment they have technically evaluated the exploit. Payment will be made by bank transfer or, for those who value their anonymity, in Bitcoin/Monero.
All researchers who are Israeli citizens should know that the selling of exploits is a process supervised by the Israeli Defense Export Control Agency (DECA). Regardless of whether you operate from Israel or live anywhere else around the globe, DECA has the privilege to invoke the mediation clause, and the Agency has a duty to exercise that privilege (even though it does not, even after the critical review of the State Comptroller on this subject). Exploits came under DECA's supervision as of January 2018, pursuant to the revision of the Wassenaar Arrangement (The Wassenaar Arrangement on Export Controls for Conventional Arms and Dual-Use Goods and Technologies). The selling of an exploit is a process defined by the Arrangement as a transaction that requires supervision, so this requirement has automatically become Israeli legislation.
You will face your main dilemma if the State of Israel should be interested in your exploit. In that case, DECA may, theoretically, refuse to authorize the selling of your exploit to Zerodium and compel you to hand the exploit over to the state (and there is no chance IMOD will ever pay you a million dollars or two million dollars for it). This dilemma stems from the fact that Israel has no structured vulnerability/exploit exposure procedure like the procedures in place in some western countries. Consequently, an Israeli researcher is at the mercy of IMOD in this context. In this regard, a vulnerability/exploit is just like any other weapon system, with one difference – it is doubtful whether Zerodium provides end-user certificates (namely, an undertaking as to whom they would sell the exploits to).
It should be noted that the last two paragraphs are theoretical, as practically, the price of a million or two million dollars is high enough to encourage researchers to bypass DECA. For an exploit, you do not even need a suitcase.
Bug Bounty vulnerability hunting software products pay nice rewards, but nothing like the amounts offered by Zerodium – the zero-day exploit vendor. The company sells vulnerabilities as a permit, thereby reducing the vulnerability/exploit cost for the end user.
The latest announcement regarding the platform provided a price list for exploits. Well, the price for an Apple iOS remote jailbreak (zero-click) with persistence amounts to two million dollars. The same exploit with one click will produce $1.5 million. An exploit for WhatsApp will produce a million dollars and an exploit for Chrome or Safari will produce about $500,000. An exploit for Windows will produce a million dollars. The company undertakes to pay within one week of the moment they have technically evaluated the exploit. Payment will be made by bank transfer or, for those who value their anonymity, in Bitcoin/Monero.
All researchers who are Israeli citizens should know that the selling of exploits is a process supervised by the Israeli Defense Export Control Agency (DECA). Regardless of whether you operate from Israel or live anywhere else around the globe, DECA has the privilege to invoke the mediation clause, and the Agency has a duty to exercise that privilege (even though it does not, even after the critical review of the State Comptroller on this subject). Exploits came under DECA's supervision as of January 2018, pursuant to the revision of the Wassenaar Arrangement (The Wassenaar Arrangement on Export Controls for Conventional Arms and Dual-Use Goods and Technologies). The selling of an exploit is a process defined by the Arrangement as a transaction that requires supervision, so this requirement has automatically become Israeli legislation.
You will face your main dilemma if the State of Israel should be interested in your exploit. In that case, DECA may, theoretically, refuse to authorize the selling of your exploit to Zerodium and compel you to hand the exploit over to the state (and there is no chance IMOD will ever pay you a million dollars or two million dollars for it). This dilemma stems from the fact that Israel has no structured vulnerability/exploit exposure procedure like the procedures in place in some western countries. Consequently, an Israeli researcher is at the mercy of IMOD in this context. In this regard, a vulnerability/exploit is just like any other weapon system, with one difference – it is doubtful whether Zerodium provides end-user certificates (namely, an undertaking as to whom they would sell the exploits to).
It should be noted that the last two paragraphs are theoretical, as practically, the price of a million or two million dollars is high enough to encourage researchers to bypass DECA. For an exploit, you do not even need a suitcase.