Cybertech Presents: The Next Cyber Revolution
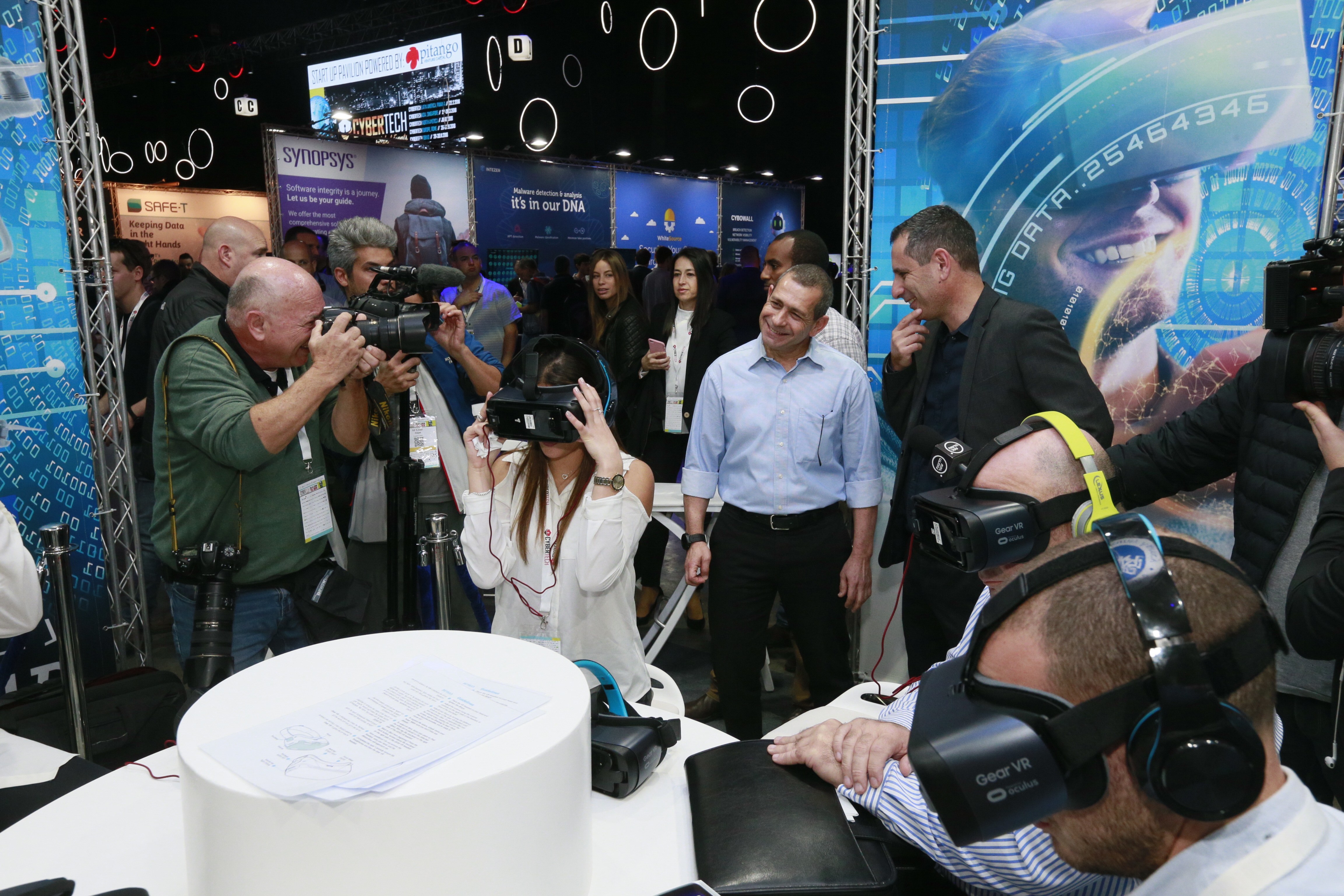
Cybertech Tel Aviv 2018 Conference & Exhibition, held this week at the Tel Aviv Convention Center, drew 15,000 visitors from around the globe, and over 200 companies exhibited their innovative technologies and solutions in the cyber domain. Special coverage
IsraelDefense
| 02/02/2018
Some 15,000 people participated at this year's Cybertech Tel Aviv, the largest cyber event outside the USA. During the course of the three-day event, 170 high-profile speakers from around the world addressed the conference, and 125 companies along with 90 startups showcased their technologies and solutions at the exhibition.

Yigal Unna, Director-General of the Israel National Cyber Directorate (INCD), spoke at the opening plenary and addressed the cyber threats facing countries today. "Cyber threats are becoming darker, and Israel makes no exception. One of the most significant solutions is the formation of an international cyber coalition, as part of the comprehensive approach."

Dr. Eviatar Matania, the first Director-General of the INCD who recently stepped down after six years in office, reiterated the necessity of an international cyber coalition. "The cyber threat is a global one, which requires global collaborations. Cybertech is the Israeli opportunity to generate it. People from all over the world come to Israel to build this collaboration."
In a special ceremony, Dr. Matania was awarded an honorary plaque for his important contribution in establishing Israel's National Cyber Directorate and his unwavering support to the cyber community in Israel.
ISA Chief Nadav Argaman visited the exhibition and said that his organization thwarted many cyber attacks on Israel, which originated from countries all over the world.

Gil Shwed, Founder and CEO of Check Point Software Technologies, said that today we encounter the 5th-generation of attacks, with combined viruses, as the mobile environment is challenging. He emphasized that it is imperative to develop innovative, sophisticated, sixth-generation defenses, in order to defeat today's attacks.

"Israel is a cyber superpower," said Gen. (ret.) David Petraeus, former head of the CIA, in a joint discussion on cyber threats and solutions with Nadav Tsafrir, CEO of TEAM8 and Former commander of the IDF's elite 8200 Unit. "The partnership between the United States and Israel has given the option to cope together against the counter threats, which is extremely important. The collaboration reaches new heights time and time again, far beyond what is being published in the media," Petraeus said.

According to Marc Van Zadelhof, General Manager of IBM Security, "There is a war coming of bad AI vs. good AI. We must treat the security as an immune system, holistically. AI impacts our customers, like Watson, which revealed new realms of search in the AI world. Prepare for the inevitable. Study user behavior, train machinery to reduce false positives, as part of an eco-system of apps driven by AI."

Udi Mokady, Chairman & CEO of CyberArk: "The speeding developments affect the topline of the organization. Modern architecture allows often releases, managed by humans, codes and machines. However, security is not keeping up, since most do not have the knowledge regarding how to secure the cloud's architecture. Credentials are used to take over domains. It allows much more opportunities for hackers, while the attack surface is wide for infections."

Cyril Voisin, Executive Security Advisor at Microsoft's Enterprise Cybersecurity Group: "There are four domains to the modern security approach: security management, identity and access management, credentials and information encryption. The technology around the enterprises, in terms of detection and response, like a black box to detect exactly what happened. The attack will try to access the data, but the black box will have the behavior analysis, ATA."

Michele Iacovone, Senior Vice President, Chief Information Security and Fraud Officer at Intuit: "Making the eco system secure is our goal. There is a transformation from traditional security into the cloud. The sophistication of the attacks improves so we have to use the entire surface of the eco system, getting the employees and engineers to work as a team, expending it to our third parties."

Maj. Gen. (ret.) Yiftch Ron Tal, Chairman of the Board of Directors of Israel Electric Corporation: "Systems of energy storage will become more effective in the future. The abilities will be implemented and we would be advancing towards a world with almost unlimited energy and store it in a cost-effective manner. Each of us will become a consumer, and we will move from the conventional form. From smart grid to smart net – autonomous and dynamic, like the internet of electricity, IOE, which will be supported by Blockchain technology; a fast solution without mediators. However, every tech might be hacked, especially if everyone is connected. The significance of the attack would even grow and the options would become endless. Therefore, we must change the old cyber conventions and include all possible vectors. Complementary models must also be developed to detect anomalies quickly."

Mr. Naftali Bennett, Israeli Minister of Education and Diaspora Affairs: "Today everything is connected to the cloud: services, water, electricity, cars, our bodies, and soon our brains. In a broader level, it is just the tip of the iceberg. A big and growing bulk of future warfare would be cyber warfare. This world is only at its beginning."

Dr. Erel N. Margalit, Founder and Chairman of JVP and a former member of Knesset, talked about the Iranian cyber threat. "Iran's cyber threat to the region is crucial. The Iranian nuclear threat is a future threat, but the Iranian cyber threat is an immediate threat, and Israel’s civil infrastructure in Israel is exposed and vulnerable. Eleven Revolutionary Guard strike groups attack Israeli nuclear researchers and civilian infrastructure on a daily basis. We know of many attacks in the region and in other parts of the world, on civil and military targets, many of them financed by Iran."

John Delk, Chief Product Officer, and GM of Security Product Group at Microfocus: "Enterprise Security is similar to a 3D chess. Users, application and data are the players. As new vulnerabilities arise, we must solve the security issues and encrypt information. The arena forces us to protect all three layers, pervasive across all aspects of enterprise. Data management is the most important to protect all three."
Among the other keynote speakers at the event:

Grant Waterfall, EMEA Cybersecurity and Privacy Leader at PwC

Michal Braverman-Blumenstyk, CTO, Cloud & Enterprise Security at Microsoft

Esti Peshin, General Manager of IAI's Cyber Division


Dr. Orna Berry, Vice President at Dell EMC, and Dr. Yaniv Harel, GM of Dell EMC Cyber Solutions Group

Dr. Dorit Dor, VP of Products at Check Point Software Technologies
Several special events were held throughout the conference, focusing on pressing issues in the cyber realm, including cyber challenges in the health sector, aviation and transportation cybersecurity, seaports and maritime cybersecurity, international cooperation in order to deal with global cyber threats, and more.






During the event, Dell EMC Cyber Solutions Group and TSG launched a joint service for managing and monitoring cyber events in organizations.

As mentioned, over 200 companies and organizations participated in the exhibition.




As part of Cybertech Tel Aviv 2018, a startup competition was held, powered by YL Ventures, to select the most innovative startup in the cybersecurity field. The winner of this year's competition was Protego, which provides full lifecycle security for serverless applications from deployment to runtime. The winners received two entry tickets to the RSA conference.

Photography: Gilad Kavalerchik
Cybertech Tel Aviv 2018 Conference & Exhibition, held this week at the Tel Aviv Convention Center, drew 15,000 visitors from around the globe, and over 200 companies exhibited their innovative technologies and solutions in the cyber domain. Special coverage
Some 15,000 people participated at this year's Cybertech Tel Aviv, the largest cyber event outside the USA. During the course of the three-day event, 170 high-profile speakers from around the world addressed the conference, and 125 companies along with 90 startups showcased their technologies and solutions at the exhibition.
Yigal Unna, Director-General of the Israel National Cyber Directorate (INCD), spoke at the opening plenary and addressed the cyber threats facing countries today. "Cyber threats are becoming darker, and Israel makes no exception. One of the most significant solutions is the formation of an international cyber coalition, as part of the comprehensive approach."
Dr. Eviatar Matania, the first Director-General of the INCD who recently stepped down after six years in office, reiterated the necessity of an international cyber coalition. "The cyber threat is a global one, which requires global collaborations. Cybertech is the Israeli opportunity to generate it. People from all over the world come to Israel to build this collaboration."
In a special ceremony, Dr. Matania was awarded an honorary plaque for his important contribution in establishing Israel's National Cyber Directorate and his unwavering support to the cyber community in Israel.
ISA Chief Nadav Argaman visited the exhibition and said that his organization thwarted many cyber attacks on Israel, which originated from countries all over the world.
Gil Shwed, Founder and CEO of Check Point Software Technologies, said that today we encounter the 5th-generation of attacks, with combined viruses, as the mobile environment is challenging. He emphasized that it is imperative to develop innovative, sophisticated, sixth-generation defenses, in order to defeat today's attacks.
"Israel is a cyber superpower," said Gen. (ret.) David Petraeus, former head of the CIA, in a joint discussion on cyber threats and solutions with Nadav Tsafrir, CEO of TEAM8 and Former commander of the IDF's elite 8200 Unit. "The partnership between the United States and Israel has given the option to cope together against the counter threats, which is extremely important. The collaboration reaches new heights time and time again, far beyond what is being published in the media," Petraeus said.

According to Marc Van Zadelhof, General Manager of IBM Security, "There is a war coming of bad AI vs. good AI. We must treat the security as an immune system, holistically. AI impacts our customers, like Watson, which revealed new realms of search in the AI world. Prepare for the inevitable. Study user behavior, train machinery to reduce false positives, as part of an eco-system of apps driven by AI."

Udi Mokady, Chairman & CEO of CyberArk: "The speeding developments affect the topline of the organization. Modern architecture allows often releases, managed by humans, codes and machines. However, security is not keeping up, since most do not have the knowledge regarding how to secure the cloud's architecture. Credentials are used to take over domains. It allows much more opportunities for hackers, while the attack surface is wide for infections."

Cyril Voisin, Executive Security Advisor at Microsoft's Enterprise Cybersecurity Group: "There are four domains to the modern security approach: security management, identity and access management, credentials and information encryption. The technology around the enterprises, in terms of detection and response, like a black box to detect exactly what happened. The attack will try to access the data, but the black box will have the behavior analysis, ATA."
Michele Iacovone, Senior Vice President, Chief Information Security and Fraud Officer at Intuit: "Making the eco system secure is our goal. There is a transformation from traditional security into the cloud. The sophistication of the attacks improves so we have to use the entire surface of the eco system, getting the employees and engineers to work as a team, expending it to our third parties."
Maj. Gen. (ret.) Yiftch Ron Tal, Chairman of the Board of Directors of Israel Electric Corporation: "Systems of energy storage will become more effective in the future. The abilities will be implemented and we would be advancing towards a world with almost unlimited energy and store it in a cost-effective manner. Each of us will become a consumer, and we will move from the conventional form. From smart grid to smart net – autonomous and dynamic, like the internet of electricity, IOE, which will be supported by Blockchain technology; a fast solution without mediators. However, every tech might be hacked, especially if everyone is connected. The significance of the attack would even grow and the options would become endless. Therefore, we must change the old cyber conventions and include all possible vectors. Complementary models must also be developed to detect anomalies quickly."
Mr. Naftali Bennett, Israeli Minister of Education and Diaspora Affairs: "Today everything is connected to the cloud: services, water, electricity, cars, our bodies, and soon our brains. In a broader level, it is just the tip of the iceberg. A big and growing bulk of future warfare would be cyber warfare. This world is only at its beginning."
Dr. Erel N. Margalit, Founder and Chairman of JVP and a former member of Knesset, talked about the Iranian cyber threat. "Iran's cyber threat to the region is crucial. The Iranian nuclear threat is a future threat, but the Iranian cyber threat is an immediate threat, and Israel’s civil infrastructure in Israel is exposed and vulnerable. Eleven Revolutionary Guard strike groups attack Israeli nuclear researchers and civilian infrastructure on a daily basis. We know of many attacks in the region and in other parts of the world, on civil and military targets, many of them financed by Iran."
John Delk, Chief Product Officer, and GM of Security Product Group at Microfocus: "Enterprise Security is similar to a 3D chess. Users, application and data are the players. As new vulnerabilities arise, we must solve the security issues and encrypt information. The arena forces us to protect all three layers, pervasive across all aspects of enterprise. Data management is the most important to protect all three."
Among the other keynote speakers at the event:

Grant Waterfall, EMEA Cybersecurity and Privacy Leader at PwC

Michal Braverman-Blumenstyk, CTO, Cloud & Enterprise Security at Microsoft
Esti Peshin, General Manager of IAI's Cyber Division
Dr. Orna Berry, Vice President at Dell EMC, and Dr. Yaniv Harel, GM of Dell EMC Cyber Solutions Group
Dr. Dorit Dor, VP of Products at Check Point Software Technologies
Several special events were held throughout the conference, focusing on pressing issues in the cyber realm, including cyber challenges in the health sector, aviation and transportation cybersecurity, seaports and maritime cybersecurity, international cooperation in order to deal with global cyber threats, and more.
During the event, Dell EMC Cyber Solutions Group and TSG launched a joint service for managing and monitoring cyber events in organizations.

As mentioned, over 200 companies and organizations participated in the exhibition.
As part of Cybertech Tel Aviv 2018, a startup competition was held, powered by YL Ventures, to select the most innovative startup in the cybersecurity field. The winner of this year's competition was Protego, which provides full lifecycle security for serverless applications from deployment to runtime. The winners received two entry tickets to the RSA conference.
Photography: Gilad Kavalerchik



